NSSCTF-[NCTF 2021]狗狗的秘密
创始人
2025-06-01 11:35:43
题目链接:NSSCTF
根据题目标签,这道题考了SMC,xtea和base47。
无壳,载入IDA,看main函数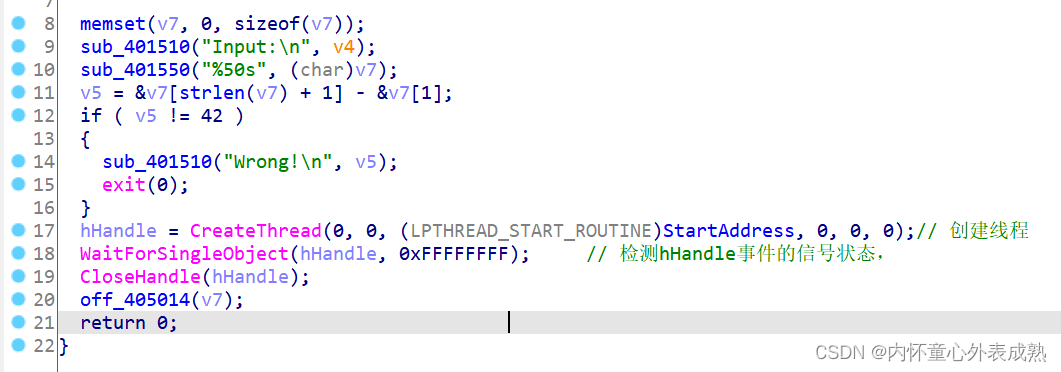 可知输入长度是42。然后创造了新线程,进入线程开始地址'StartAddress'。
可知输入长度是42。然后创造了新线程,进入线程开始地址'StartAddress'。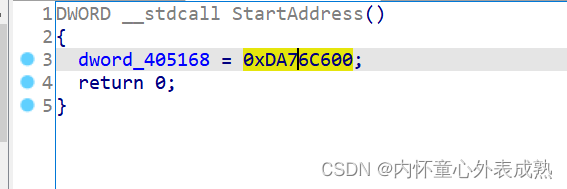
是一个赋值语句就没别的了,很迷。在进入‘off_405014’看一看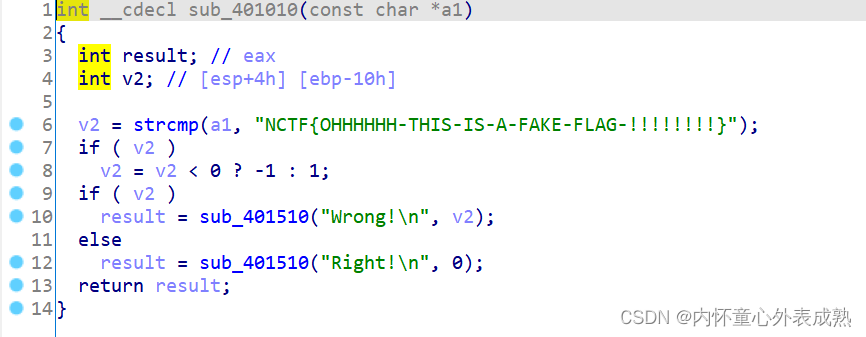 发现是个fake_flag。好像这个main函数没有什么太有用的...
发现是个fake_flag。好像这个main函数没有什么太有用的...
那对’off_405014‘交叉引用,进入到下图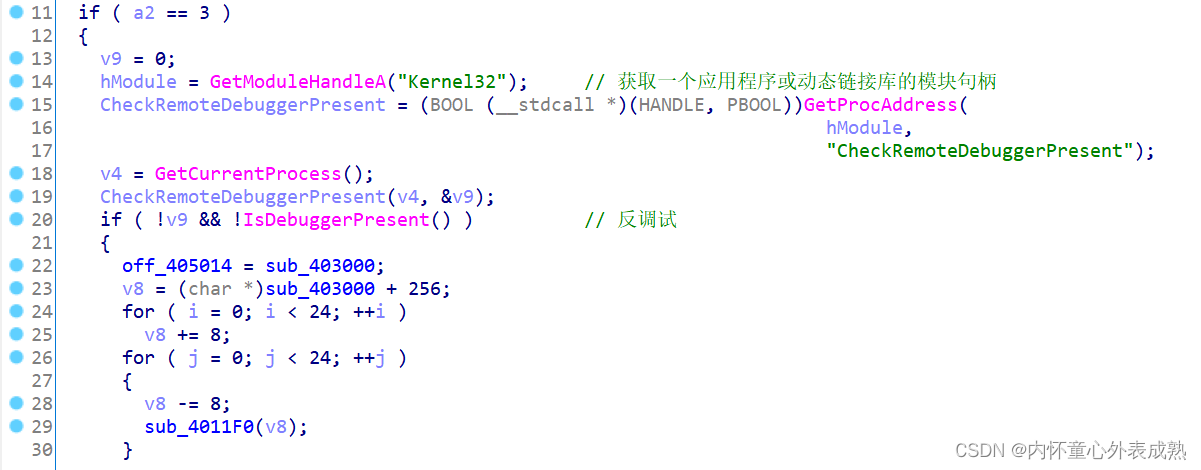
主要看if语句,有个反调试和赋值,看一下那个sub_403000函数: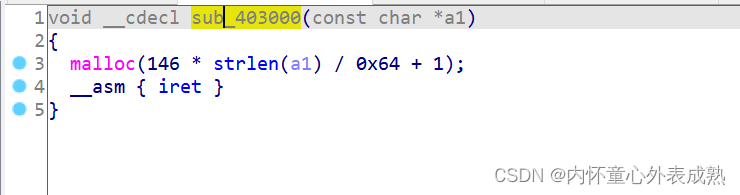
很诡异,看一看sub_403000汇编代码,正好在SMC代码区。所以他应该最后会被解密为一个完成函数代码。回去继续观察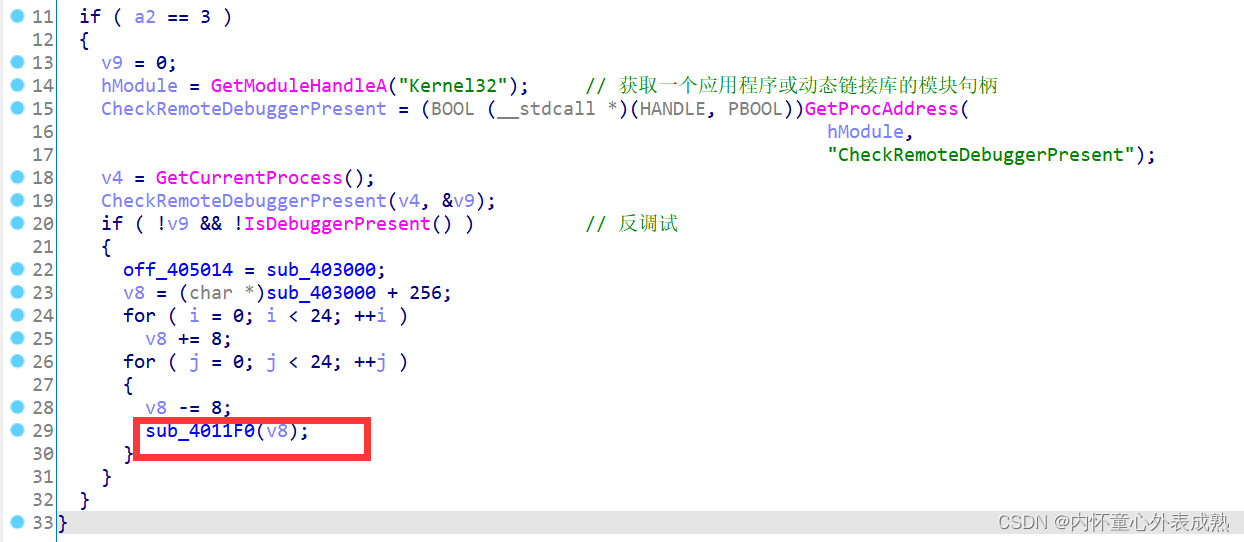
进入这个红框里的函数,是一个xtea加密,并且是对v8操作,而v8和sub_403000有关,所以通过xtea进行解密。所以动态调试,自解密。
因为有反调试,patch掉。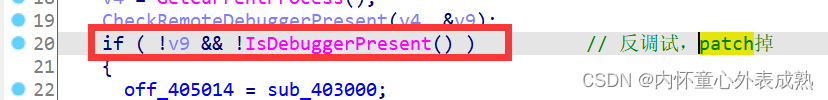
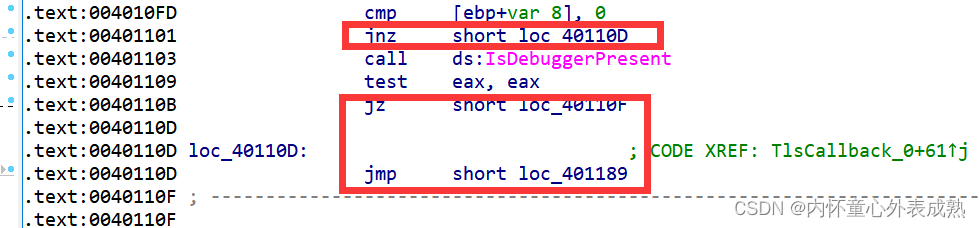 patch这些跳转,使直接执行if的子句。
patch这些跳转,使直接执行if的子句。
sub_4011C0函数也有反调试,nop掉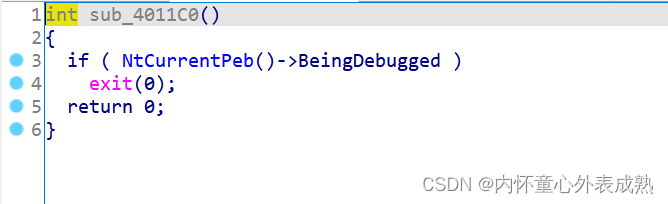
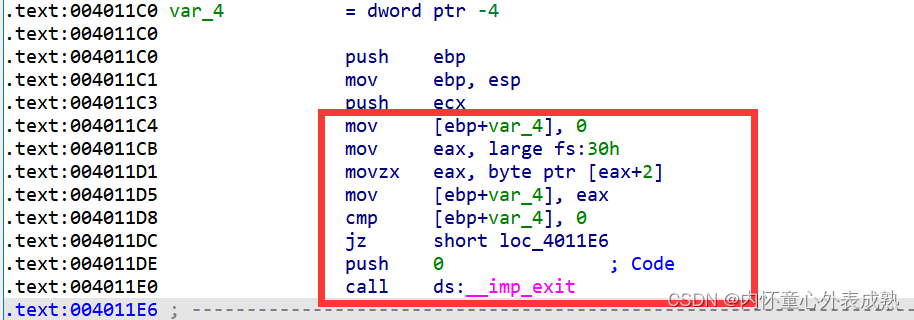 patch反调试完保存一下,在sub_403000处下个断点(smc自解密执行在这个断点之前),动态调试。
patch反调试完保存一下,在sub_403000处下个断点(smc自解密执行在这个断点之前),动态调试。
进入sub_403000。把那些数据按热键u未定义,再热键c改为汇编代码。如下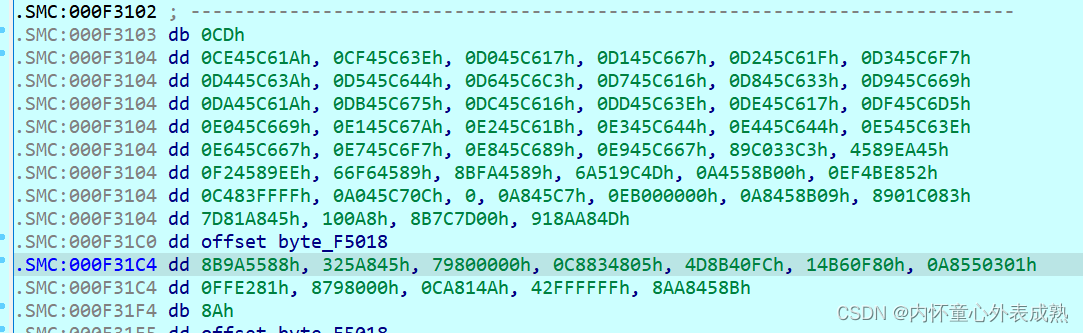
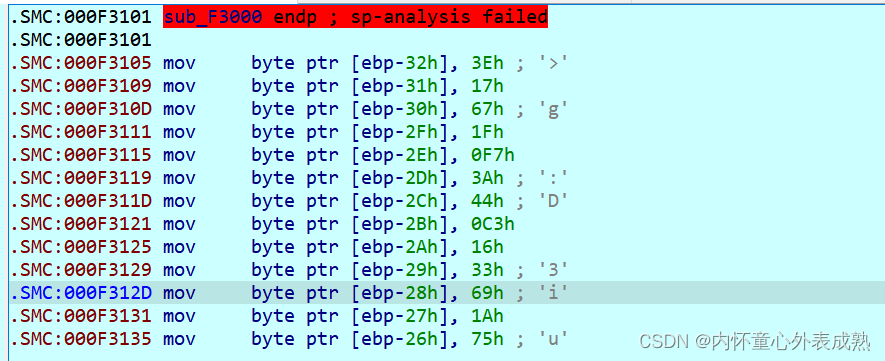 但是f5无法识别,可以看到上面有红色警告,堆栈不平衡。在红色提醒那里快捷键alt+p,
但是f5无法识别,可以看到上面有红色警告,堆栈不平衡。在红色提醒那里快捷键alt+p,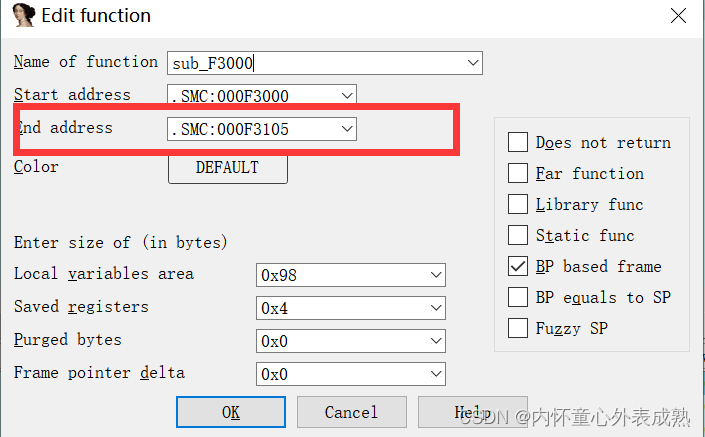
修改end address到此sub_403000函数的最后位置就可以f5了,位置如下: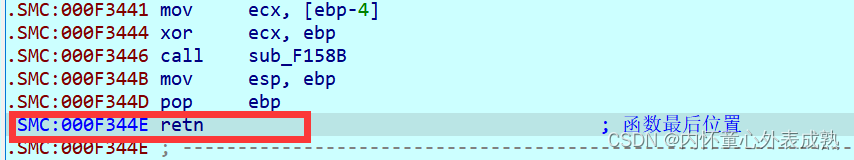
f5查看伪代码
void __cdecl sub_2C3000(const char *flag)
{signed int v1; // [esp+0h] [ebp-98h]unsigned int v2; // [esp+10h] [ebp-88h]signed int v3; // [esp+1Ch] [ebp-7Ch]int v4; // [esp+2Ch] [ebp-6Ch]int v5; // [esp+2Ch] [ebp-6Ch]char v6; // [esp+32h] [ebp-66h]signed int Size; // [esp+34h] [ebp-64h]unsigned int v8; // [esp+38h] [ebp-60h]int k; // [esp+38h] [ebp-60h]unsigned __int8 *v10; // [esp+3Ch] [ebp-5Ch]int i; // [esp+40h] [ebp-58h]signed int j; // [esp+40h] [ebp-58h]signed int l; // [esp+40h] [ebp-58h]signed int m; // [esp+40h] [ebp-58h]signed int n; // [esp+40h] [ebp-58h]char v16[62]; // [esp+44h] [ebp-54h]int v17; // [esp+82h] [ebp-16h]int v18; // [esp+86h] [ebp-12h]int v19; // [esp+8Ah] [ebp-Eh]int v20; // [esp+8Eh] [ebp-Ah]__int16 v21; // [esp+92h] [ebp-6h]v2 = strlen(flag);Size = 0x92 * v2 / 0x64 + 1;v3 = 0;v10 = (unsigned __int8 *)malloc(Size);v16[0] = 82;v16[1] = -61;v16[2] = 26;v16[3] = -32;v16[4] = 22;v16[5] = 93;v16[6] = 94;v16[7] = -30;v16[8] = 103;v16[9] = 31;v16[10] = 31;v16[11] = 6;v16[12] = 6;v16[13] = 31;v16[14] = 23;v16[15] = 6;v16[16] = 15;v16[17] = -7;v16[18] = 6;v16[19] = 103;v16[20] = 88;v16[21] = -78;v16[22] = -30;v16[23] = -116;v16[24] = 15;v16[25] = 42;v16[26] = 6;v16[27] = -119;v16[28] = -49;v16[29] = 42;v16[30] = 6;v16[31] = 31;v16[32] = -104;v16[33] = 26;v16[34] = 62;v16[35] = 23;v16[36] = 103;v16[37] = 31;v16[38] = -9;v16[39] = 58;v16[40] = 68;v16[41] = -61;v16[42] = 22;v16[43] = 51;v16[44] = 105;v16[45] = 26;v16[46] = 117;v16[47] = 22;v16[48] = 62;v16[49] = 23;v16[50] = -43;v16[51] = 105;v16[52] = 122;v16[53] = 27;v16[54] = 68;v16[55] = 68;v16[56] = 62;v16[57] = 103;v16[58] = -9;v16[59] = -119;v16[60] = 103;v16[61] = -61;v17 = 0;v18 = 0;v19 = 0;v20 = 0;v21 = 0;memset(v10, 0, Size);v8 = 0;for ( i = 0; i < 256; ++i ){v6 = byte_2C5018[i];byte_2C5018[i] = byte_2C5018[(i + *((unsigned __int8 *)&dword_2C5168 + i % 4)) % 256];byte_2C5018[(i + *((unsigned __int8 *)&dword_2C5168 + i % 4)) % 256] = v6;}while ( v8 < strlen(flag) ){v4 = flag[v8];for ( j = 0x92 * v2 / 0x64; ; --j ){v5 = v4 + (v10[j] << 8);v10[j] = v5 % 47; //47进制v4 = v5 / 47;if ( j < v3 )v3 = j;if ( !v4 && j <= v3 )break;}++v8;}for ( k = 0; !v10[k]; ++k );for ( l = 0; l < Size; ++l )v10[l] = byte_2C5118[v10[k++]]; #关键while ( l < Size )v10[l++] = 0;v1 = strlen((const char *)v10);for ( m = 0; m < v1; ++m )v10[m] ^= byte_2C5018[v10[m]]; #关键for ( n = 0; n < v1; ++n ){if ( v10[n] != (unsigned __int8)v16[n] ) //比较{sub_2C1510("Wrong!\n", v1);exit(0);}}sub_2C1510("Right!\n", v1);
}这里倒着观察,已知v10数组已知,并且是int8类型,所以从0-256爆破,然后在看他在byte_2C5118中的位置就可以求出47进制形式。
#byte_F5018
key1=[0x21, 0x43, 0x65, 0x87, 0x09, 0x21, 0x43, 0x65, 0xA2, 0x9B,0xF4, 0xDF, 0xAC, 0x7C, 0xA1, 0xC6, 0x16, 0xD0, 0x0F, 0xDD,0xDC, 0x73, 0xC5, 0x6B, 0xD1, 0x96, 0x47, 0xC2, 0x26, 0x67,0x4E, 0x41, 0x82, 0x20, 0x56, 0x9A, 0x6E, 0x33, 0x92, 0x88,0x29, 0xB5, 0xB4, 0x71, 0xA9, 0xCE, 0xC3, 0x34, 0x50, 0x59,0xBF, 0x2D, 0x57, 0x22, 0xA6, 0x30, 0x04, 0xB2, 0xCD, 0x36,0xD5, 0x68, 0x4D, 0x5B, 0x45, 0x9E, 0x85, 0xCF, 0x9D, 0xCC,0x61, 0x78, 0x32, 0x76, 0x31, 0xE3, 0x80, 0xAD, 0x39, 0x4F,0xFA, 0x72, 0x83, 0x4C, 0x86, 0x60, 0xB7, 0xD7, 0x63, 0x0C,0x44, 0x35, 0xB3, 0x7B, 0x19, 0xD4, 0x69, 0x08, 0x0B, 0x1F,0x3D, 0x11, 0x79, 0xD3, 0xEE, 0x93, 0x42, 0xDE, 0x23, 0x3B,0x5D, 0x8D, 0xA5, 0x77, 0x5F, 0x58, 0xDB, 0x97, 0xF6, 0x7A,0x18, 0x52, 0x15, 0x74, 0x25, 0x62, 0x2C, 0x05, 0xE8, 0x0D,0x98, 0x2A, 0x43, 0xE2, 0xEF, 0x48, 0x87, 0x49, 0x1C, 0xCA,0x2B, 0xA7, 0x8A, 0x09, 0x81, 0xE7, 0x53, 0xAA, 0xFF, 0x6F,0x8E, 0x91, 0xF1, 0xF0, 0xA4, 0x46, 0x3A, 0x7D, 0x54, 0xEB,0x2F, 0xC1, 0xC0, 0x0E, 0xBD, 0xE1, 0x6C, 0x64, 0xBE, 0xE4,0x02, 0x3C, 0x5A, 0xA8, 0x9F, 0x37, 0xAF, 0xA0, 0x13, 0xED,0x1B, 0xEC, 0x8B, 0x3E, 0x7E, 0x27, 0x99, 0x75, 0xAB, 0xFE,0xD9, 0x3F, 0xF3, 0xEA, 0x70, 0xF7, 0x95, 0xBA, 0x1D, 0x40,0xB0, 0xF9, 0xE5, 0xF8, 0x06, 0xBC, 0xB6, 0x03, 0xC9, 0x10,0x9C, 0x2E, 0x89, 0x5C, 0x7F, 0xB1, 0x1A, 0xD6, 0x90, 0xAE,0xDA, 0xE6, 0x5E, 0xB9, 0x84, 0xE9, 0x55, 0xBB, 0xC7, 0x0A,0xE0, 0x66, 0xF2, 0xD8, 0xCB, 0x00, 0x12, 0xB8, 0x17, 0x94,0x6A, 0x4A, 0x01, 0x24, 0x14, 0x51, 0x07, 0x65, 0x21, 0xC8,0x38, 0xFD, 0x8F, 0xC4, 0xF5, 0xFC]
#byte_F5118
key2=[ 0xA7, 0x1C, 0x7E, 0xAF, 0xD9, 0xC2, 0xC0, 0xBE, 0x1F, 0x45,0x9A, 0x85, 0x26, 0xE3, 0x87, 0xC3, 0x21, 0xE0, 0x95, 0x10,0x71, 0x70, 0x02, 0x75, 0x35, 0xA5, 0x1D, 0x0D, 0x2F, 0xEE,0x25, 0x7B, 0xB5, 0x82, 0x66, 0x8D, 0xDB, 0x53, 0x3A, 0x29,0xD4, 0x43, 0x99, 0x97, 0x9D, 0xE8, 0x49, 0x00]v10=[82, 195, 26, 224, 22, 93, 94, 226, 103, 31, 31, 6, 6, 31, 23, 6, 15, 249, 6, 103, 88, 178, 226, 140, 15, 42, 6, 137, 207, 42, 6, 31, 152, 26, 62, 23, 103, 31, 247, 58, 68, 195, 22, 51, 105, 26, 117, 22, 62, 23, 213, 105, 122, 27, 68, 68, 62, 103, 247, 137, 103, 195]for c in v10:for i in range(256):if c==key1[i]^i:#print(i)if i in key2:print(key2.index(i),end=' ')print(' ')这里会求到不止一个解,观看别的wp发现就是一个一个试的,根据v10这些余数可以求处flag,最终代码如下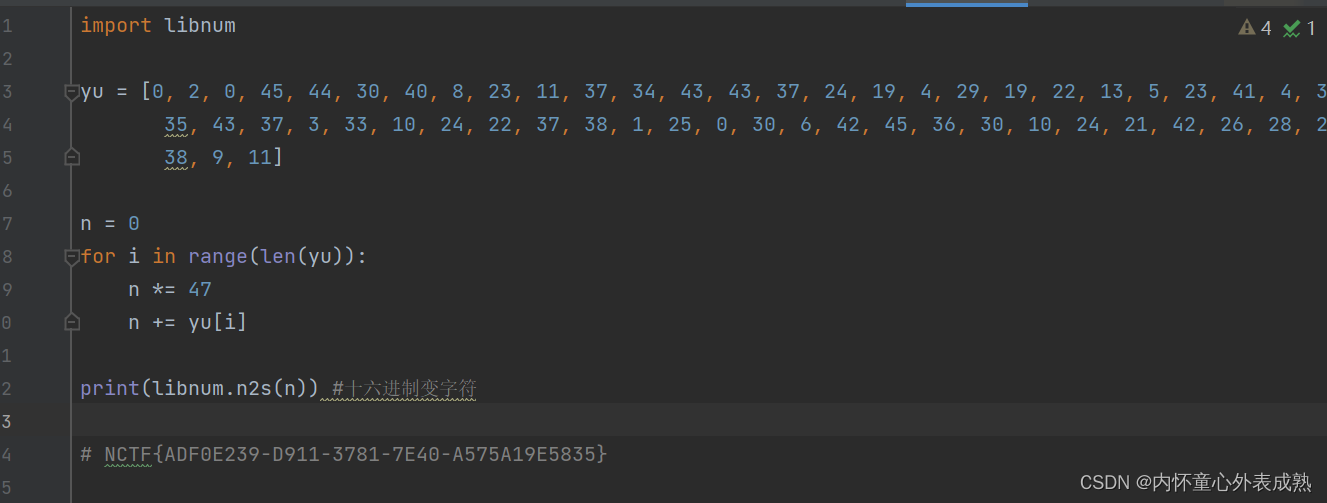
相关内容
热门资讯
苗族的传统节日 贵州苗族节日有...
【岜沙苗族芦笙节】岜沙,苗语叫“分送”,距从江县城7.5公里,是世界上最崇拜树木并以树为神的枪手部落...
长白山自助游攻略 吉林长白山游...
昨天介绍了西坡的景点详细请看链接:一个人的旅行,据说能看到长白山天池全凭运气,您的运气如何?今日介绍...
北京的名胜古迹 北京最著名的景...
北京从元代开始,逐渐走上帝国首都的道路,先是成为大辽朝五大首都之一的南京城,随着金灭辽,金代从海陵王...
怎么样的桃花 桃花近看远看的样...
今年的“三八”妇女节,阳光明媚,踏青赏花正当时。遂与姐妹们共赴十里蓝山,与花海来一场春天的约会。十里...
应用未安装解决办法 平板应用未...
---IT小技术,每天Get一个小技能!一、前言描述苹果IPad2居然不能安装怎么办?与此IPad不...
猫咪吃了塑料袋怎么办 猫咪误食...
你知道吗?塑料袋放久了会长猫哦!要说猫咪对塑料袋的喜爱程度完完全全可以媲美纸箱家里只要一有塑料袋的响...
脚上的穴位图 脚面经络图对应的...
人体穴位作用图解大全更清晰直观的标注了各个人体穴位的作用,包括头部穴位图、胸部穴位图、背部穴位图、胳...
世界上最漂亮的人 世界上最漂亮...
此前在某网上,选出了全球265万颜值姣好的女性。从这些数量庞大的女性群体中,人们投票选出了心目中最美...
demo什么意思 demo版本...
618快到了,各位的小金库大概也在准备开闸放水了吧。没有小金库的,也该向老婆撒娇卖萌服个软了,一切只...
北京的名胜古迹 北京最著名的景...
北京从元代开始,逐渐走上帝国首都的道路,先是成为大辽朝五大首都之一的南京城,随着金灭辽,金代从海陵王...
苗族的传统节日 贵州苗族节日有...
【岜沙苗族芦笙节】岜沙,苗语叫“分送”,距从江县城7.5公里,是世界上最崇拜树木并以树为神的枪手部落...
世界上最漂亮的人 世界上最漂亮...
此前在某网上,选出了全球265万颜值姣好的女性。从这些数量庞大的女性群体中,人们投票选出了心目中最美...
长白山自助游攻略 吉林长白山游...
昨天介绍了西坡的景点详细请看链接:一个人的旅行,据说能看到长白山天池全凭运气,您的运气如何?今日介绍...
怎么样的桃花 桃花近看远看的样...
今年的“三八”妇女节,阳光明媚,踏青赏花正当时。遂与姐妹们共赴十里蓝山,与花海来一场春天的约会。十里...
demo什么意思 demo版本...
618快到了,各位的小金库大概也在准备开闸放水了吧。没有小金库的,也该向老婆撒娇卖萌服个软了,一切只...
应用未安装解决办法 平板应用未...
---IT小技术,每天Get一个小技能!一、前言描述苹果IPad2居然不能安装怎么办?与此IPad不...
脚上的穴位图 脚面经络图对应的...
人体穴位作用图解大全更清晰直观的标注了各个人体穴位的作用,包括头部穴位图、胸部穴位图、背部穴位图、胳...
猫咪吃了塑料袋怎么办 猫咪误食...
你知道吗?塑料袋放久了会长猫哦!要说猫咪对塑料袋的喜爱程度完完全全可以媲美纸箱家里只要一有塑料袋的响...
